While companies have been focused on network security and detecting threats that can impact their operating system and software, another type of attack has been quietly on the rise.
Over the last four years, firmware attacks have increased by five times, leading to a redoubling of efforts by manufacturers to address historic weaknesses in device firmware security.
Firmware attacks are more difficult to detect and address because the firmware is not included in the operating system (OS) layer of a device. It sits above that layer because it’s needed to tell the device how to load and interact with the OS.
Companies haven’t paid a lot of attention to firmware in the past because it’s been one of those areas of a device that has little visibility. Firmware is the software that tells your hardware how to operate, so it’s not something most device manufacturers want users to mess with or accidentally edit.
There’s been a lack of visibility by the OS and user into the firmware layer, which makes it the perfect place for hackers to hide. Attackers can often continue conducting persistent attacks, putting backdoors into the system at the firmware level, and it’s undetectable by normal means like antivirus.
Why Has Firmware Become a Target?
Hackers are always looking for the easiest way into a device and network. This is often in the place where people are looking, which makes firmware a prime target.
Here are some of the factors that have caused the dramatic rise in firmware attacks:
- The firmware layer lacks user transparency
- Manufacturers haven’t always adequately addressed firmware security
- Even if an attack is known to the user, they often can’t detect where it is if it’s hidden in the firmware
- Firmware offers a rich attack environment with the ability to take over the entire device
So, if you lack visibility into the firmware layer, is there anything you can do to prevent attacks? Yes, there are several things you can do to help prevent a firmware attack on your devices.
Security Steps to Take to Protect Device Firmware
Keep Firmware Updated
Firmware updates can easily go unapplied because they aren’t as “flashy” as OS and software updates. They’re often hard to detect and you may even have to go into your manufacturer’s application to see if there are any waiting.
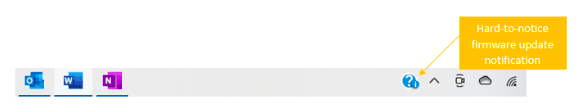
According to a recent study by Gartner, 70% of organizations that do not have a firmware update plan will be breached by 2022 due to vulnerabilities.
It’s important to ensure all firmware for your devices (PCs, servers, routers, printers, etc.) is kept updated to reduce the risk of an attack. One of the easiest ways to do this is through managed IT services, which cover all updates that your technology infrastructure needs.
When Purchasing Hardware Look for Firmware Protections
Because of the rise in firmware attacks, manufacturers like Microsoft and HP are bringing out computers with advanced firmware protection. When planning your cybersecurity focuses, make sure that you include new hardware purchases and use hardware/firmware protection as a deciding factor before you buy.
Use Email & DNS Filters to Combat Phishing
Firmware attacks originate much the same way as many other types of cyberattacks, which is through phishing emails.
It’s important to deploy preventative measures to combat phishing on two fronts. One is to keep as many phishing emails out of user inboxes as possible, and the other is to block malicious sites that users might visit from a link in a phishing email.
Email filtering helps reduce the number of dangerous phishing emails that make it in front of users, which reduces your risk of an employee getting fooled and deploying a firmware attack accidentally.
DNS filtering blocks malicious websites even after the link is clicked to protect users from falling victim to a ransomware/malware injection or fake login form.
Conduct Regular Penetration Testing of Your Systems
Often a firmware attack can go undetected, and the attacker can be stealing data or using your PC resources for quite a while. It’s important to have regular penetration testing done that also looks at the firmware layer for any breaches or backdoors that may have been put in by an attacker.
Regular testing of your systems both looks at your security to ensure you have adequate defenses and can take a thorough look at your entire system to check for any suspicious activity. The sooner you know about a breach of your firmware, the sooner you can have the issue addressed and stop the attack.
Has Your Firmware Been Quietly Breached Without You Knowing?
Connect2Geek can help your Treasure Valley business with testing and a full security audit to ensure you’re fully protected from a firmware attack.
Schedule your free consultation to learn more today! Call 208-468-4323 or reach out online.
